General Information regarding DROWN vulnerability Fix
On March 1, we have another OpenSSL vulnerability reported: DROWN. Please follow the document to know more about DROWN and DROWN Vulnerability Fix
Name: DROWN( Decrypting RSA using Obsolete and Weakened eNcryption.)
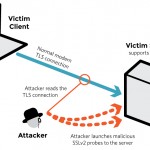
Type: Cross-protocol attack on TLS using SSLv2 (DROWN) (CVE-2016-0800).
Affected services: DROWN is a serious vulnerability that affects HTTPS and other services that rely on SSL and TLS, some of the essential cryptographic protocols for Internet security. DROWN allows attackers to break the encryption and read or steal sensitive communications, including passwords, credit card numbers, trade secrets, or financial data.
What all are Vulnerable?
– SSLv2 (Secure Sockets Layer protocol version 2.0)
– TLS (Transport Layer Security) version (1.0 – 1.2)
– Services which do not use SSLv2 , but share their RSA keys with those services which have SSLv2 support, are also vulnerable.
CVE-2016-0703 : which affected OpenSSL versions prior to 1.0.2a, 1.0.1m, 1.0.0r, and 0.9.8z
CVE-2016-0704 : This issue affected OpenSSL versions 1.0.2, 1.0.1l, 1.0.0q, 0.9.8ze and all earlier versions.
Affected Operating Systems Versions
Redhat/Centos:
Red Hat Enterprise Linux 4
Red Hat Enterprise Linux 5
Red Hat Enterprise Linux 6
Red Hat Enterprise Linux 7
The affected OS versions along with details regarding available updates(which are free of the DROWN vulnerability).
Red Hat Enterprise Linux 5 openssl-0.9.8e-39.el5_11Red Hat Enterprise Linux 5.6 openssl-0.9.8e-12.el5_6.13Red Hat Enterprise Linux 5.9 openssl-0.9.8e-26.el5_9.5Red Hat Enterprise Linux 6 openssl-1.0.1e-42.el6_7.4Red Hat Enterprise Linux 6.2 openssl-1.0.0-20.el6_2.8Red Hat Enterprise Linux 6.4 openssl-1.0.0-27.el6_4.5Red Hat Enterprise Linux 6.5 openssl-1.0.1e-16.el6_5.16Red Hat Enterprise Linux 6.6 openssl-1.0.1e-30.el6_6.12
Ubuntu distros are free from DROWN Vulnerability:
| Upstream: | needs-triage |
| Ubuntu 12.04 LTS (Precise Pangolin): | not-affected |
| Ubuntu 14.04 LTS (Trusty Tahr): | not-affected |
| Ubuntu Touch 15.04: | not-affected |
| Ubuntu Core 15.04: | not-affected |
| Ubuntu 15.10 (Wily Werewolf): | not-affected |
| Ubuntu 16.04 (Xenial Xerus): | not-affected |
Amazon Web Services (AWS)
AWS Services are not affected by this Vulnerability, but Amazon Elastic Load Balancer customers that have modified their default ELB configurations in order to explicitly accept SSLv2 should immediately follow the below steps:
The following steps can be used to enable the AWS-recommended Predefined Security Policy via the AWS Console:
- Select your load balancer (EC2 > Load Balancers).
- In the Listeners tab, click “Change” in the Cipher column.
- Ensure that the radio button for “Predefined Security Policy” is selected
- In the dropdown, select the “ELBSecurityPolicy-2015-05” policy.
- Click “Save” to apply the settings to the listener.
- Repeat these steps for each listener that is using HTTPS or SSL for each load balancer.
To identify if your server OpenSSL package is vulnerable, Redhat provides a script which can be used to check if the installed openssl version(only on Redhat or Centos servers) is vulnerable to DROWN attacks. Script file can be downloaded from here
If your server is vulnerable the script execution output will be as follows:
===========================================================
# bash DROWN-test.sh
WARNING: The installed version of openssl (openssl-<version>) is vulnerable to both general and special DROWN attack and should be upgraded!
See https://access.redhat.com/security/vulnerabilities/drown for more information.
If its not vulnerable:
The installed version of openssl (openssl-<version>) is not known to be vulnerable to DROWN.
DROWN Attack Fix:
We need to apply the available patches and the reboot the servers. If a reboot is not possible, restarting all network services that depend on openssl after applying the patches is required. A server reboot after openssl upgrade is recommended so as ensure that all services use the upgraded openssl version.
Steps:
- Upgrade openssl
# yum update openssl
- Restart all services using openssl or reboot the server(recommended)
If you need any help to fix this vulnerability feel free to email us : security [at] urolime [dot] com
![]()