Microsoft Azure is committed to providing superior care to cloud security. Azure provides high-end protection against threats and vulnerabilities. The security efforts from Azure makes the IT environment resilient to risks and attacks while safeguarding user access and preserving customer data. The security practices for Azure moreover involves encrypted transmissions, threat prevention, and management procedures.
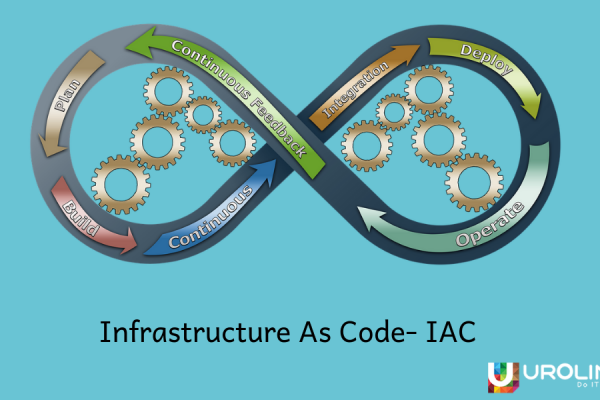
The worldwide public cloud services market is projected to grow 17.3 percent in 2019 to total $206.2 billion, up from $175.8 billion in 2018, according to Gartner, Inc. Shifting to Infrastructure-as-a-Service (IaaS) has become a burgeoning trend across most of the niches. When a user perspective is considered, an increase in demand results can result in increased requirements, vulnerabilities, and interventions. The development team should follow the security best practices for designing, deploying and managing the cloud solutions using Azure to ensure optimum quality and product deliverability. Here we are listing the security best practices followed by industry experts and clients from diverse industries.
Identity And Access Management
This entails managing user identities and access to apps, data and environments. It is permitted using the alliance of user identities in Azure Active Directory and Multi-Factor Authentication for more secure access.
Reducing Exposure To Privileged Accounts: Privileged accounts help control the data and systems of a system. In order to secure such accounts and reduce the risks of vulnerability by a malicious user, complete isolation to accounts and systems has to be implemented. For this, the optimal security practice involves placing a “least privilege” policy using Active Directory Privileged Identity Management. This allows users to limit individual access to the minutest possible number of workloads, applications, and data.
Layered Authentication Systems: Adding an additional layer of identity protection such as two-step verification, protect the application from the theft of credentials and data compromise. The organizations lacking this additional layer of protection is more susceptible to threats and such data losses. The Multi-Factor Authentication system helps define the two-step verification by facilitating conditional access. Setting up particulars decreases the occurrences of frequently asking identical questions to the users. Such requirements may include login from far away locations, differents or unapproved devices, or apps that the system considers risky.
Restricting User Access: The built-in role-based access control (RBAC) in Azure enables limiting user access. It permits allowing permissions to users, groups, and applications over various ranges. Companies running without RBAC grant more privileges to the users than required. This mispractice may lead to data compromises and in the worst case, data breaches.
Fundamentals suggested by Microsoft Azure documentation
- Treat identity as the primary security perimeter
- Centralize identity management
- Manage connected tenants
- Enable single sign-on
- Turn on Conditional Access
- Enable password management
- Enforce multi-factor verification for users
- Use role-based access control
- Lower exposure of privileged accounts
- Control locations where resources are located
- Use Azure AD for storage authentication
Data Security And Encryption
Data Protection: Azure employs industry-standard transport protocols between Microsoft data centers and user devices as well as within data centers, for the data in transit. And for data at rest, it offers a broad range of encryption capabilities up to AES-256. This affords exceptional flexibility in adopting the solution that is best suited to organizational requirements. Leveraging Azure Information Protection solution(AIP), you can manage and secure mail, documents, and delicate data that are shared with external sources. The system can distinguish between risky behavior and take corrective measures by observing the usage of protecting service using Azure RMS (Rights Management System).
Key Management: Protecting keys is crucial to defend cloud data. Toward threat review and detection, Microsoft Azure allows usage of monitoring and auditing data. This is accomplished by sending records to Azure or the user’s Security Information and Event Management (SIEM) system. With the help of Azure Key Vault, it’s easier to store encryption and passwords seamlessly.
Fundamentals suggested by Microsoft Azure documentation
- Choose a key management solution
- Manage with secure workstations
- Protect data at rest
- Protect data in transit
- Secure email, documents, and sensitive data
Network Protection
Limit Network Access: The RDP port is accessible through the web when a new virtual machine is deployed. The SSH port is open in the case of Linux virtual machines. Best security practices suggests protecting these systems to decrease the risk of unauthorized access. Azure enables the practice of network security groups (Network Security Group – NSG). Resource Manager allots NSGs to restrict access from all networks to only the essential access points. Azure virtual networks stretch the local system in the cloud via site-to-site VPN to improve the use of NSGs.
Simplify User Security: It is crucial to consider automation across multiple levels to simplify security methods and decrease human errors. Implementing a predetermined security policy can help in automating user device compliance.
Fundamentals suggested by Microsoft Azure documentation
- Use strong network controls
- Logically segment subnets
- Adopt a Zero Trust approach
- Control routing behavior
- Use virtual network appliances
- Deploy perimeter networks for security zones
- Avoid exposure to the internet with dedicated WAN links
- Optimize uptime and performance
- Disable RDP/SSH Access to virtual machines
- Secure your critical Azure service resources to only your virtual networks
Operating Systems
Threat Management: Azure advances Anti-malware for cloud services and virtual machines. This is done through the integration to intrusion identification solutions, denial of service (DDoS) attacks, regular penetration tests, data analysis tools, and machine learning. Microsoft Azure also offers scheduled scans, signature updates and real-time protection of the VMs and cloud services.
These Azure security best practices are acquired from industry experts from their thorough expertise and experimentation. Technologies and expert opinions are changing over time and hence research is a crucial element in opting the best security practices. Did we miss out anything here in this article? Let’s help each other out by contributing your ideas in the comments.
![]()